A PoV on Top 10 Cybersecurity Strategies for Secure LLM Applications
As Large Language Models (LLMs) move from being research-focused approaches to essential components of enterprise systems, new…
As Large Language Models (LLMs) move from being research-focused approaches to essential components of enterprise systems, new…
The explosion in computational complexity, networking speeds, and Artificial Intelligence is fundamentally reshaping the semiconductor industry…

The explosion in computational complexity, networking speeds, and Artificial Intelligence is fundamentally reshaping the semiconductor industry…
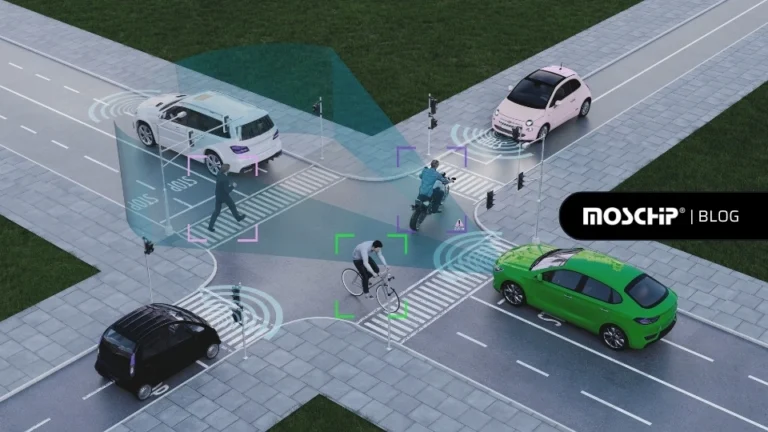
Sensor fusion combines data from cameras, LiDAR, RADAR, and other sensors to help vehicles perceive their surroundings…
In today’s fast-paced silicon industry, hardware design is under constant pressure to innovate, iterate, and ship faster…

Bluetooth Low Energy (BLE) has quietly become one of the most widely used technologies for wirelessly connecting devices and many companies…

Predictive maintenance is a key component of the Industrial Internet of Things (IIoT), shifting from reactive fixes and fixed schedules to proactive…
The Industrial Internet of Things (IIoT), through distributed systems, autonomous control, and real-time intelligence, has transformed…
Autonomous vehicles rely on high-quality data annotation to train AI/ML models for safe and intelligent driving. This blog explores how sensor data…

This blog explores key strategies for designing ultra-low-power thermostats, focusing on both hardware and firmware optimization. It covers…


Know how we have helped our client get more safety rating for their latest auctomobiles launched!